Uncategorized
what makes an identification replica appear authentic? Best Guide
Decoding Authenticity: What Makes an Identification Replica Appear Genuine?
Introduction: The Dark Art of Counterfeiting and Assessing Authenticity
The world of identification document manufacturing is plagued by counterfeiting – a persistent and evolving issue. The ability to create replicas that convincingly resemble originals, sometimes surprisingly well, presents significant challenges for authorities, businesses, and individuals. Understanding what makes an “ what makes an identification replica appear authentic ” (replica identification) appear genuine is crucial, whether you’re a verification professional, an investigator, or simply someone questioning a document’s legitimacy.
This in-depth guide explores the factors contributing to the appearance of authenticity in replica identifications, emphasizing advanced fabrication techniques and evaluation criteria. We’ll also examine the legal implications and risks associated with possessing or using counterfeit documents.
1. Fabrication Technologies: How Replicas Achieve a Realistic Look
The core of creating convincing replica identifications lies in advanced manufacturing technologies. Several techniques are employed, each contributing to the document’s appearance and characteristics:
- High-Quality Offset Printing: Modern offset printing capabilities allow for the reproduction of fine details and vibrant colors, often indistinguishable from original prints on official documents.
- Laser Technology: For intricate engraving of patterns and security features, laser printers offer unparalleled precision, crucial for replicating security markings on identifications.
- Advanced Polymer Use: “ fake nevada id identical dmv polycarbonate ” (fake Nevada ID identical to DMV polycarbonate), “ fake california id identical dmv polycarbonate ” (fake California ID identical to DMV polycarbonate), and other identifications fabricated in polycarbonate are particularly prized for their resistance to manipulation, durability, and ability to support high-quality printing. Polycarbonate mimics the appearance of the material used in official documents precisely.
- Micro-Text and Complex Patterns: Contemporary counterfeiters increasingly incorporate micro-text and complex patterns, difficult to reproduce without specialized equipment, enhancing the illusion of authenticity.
- Varnishing Techniques: Specialized varnishes applied to some documents create a glossy, deep effect, mirroring the UV protection and security coatings found in genuine documents.
2. Evaluation Criteria: What Experts Look For
Even with advanced fabrication techniques, a replica identification cannot be perfect. Verification experts meticulously examine for subtle anomalies that reveal the document’s counterfeit nature. Here’s what they scrutinize:
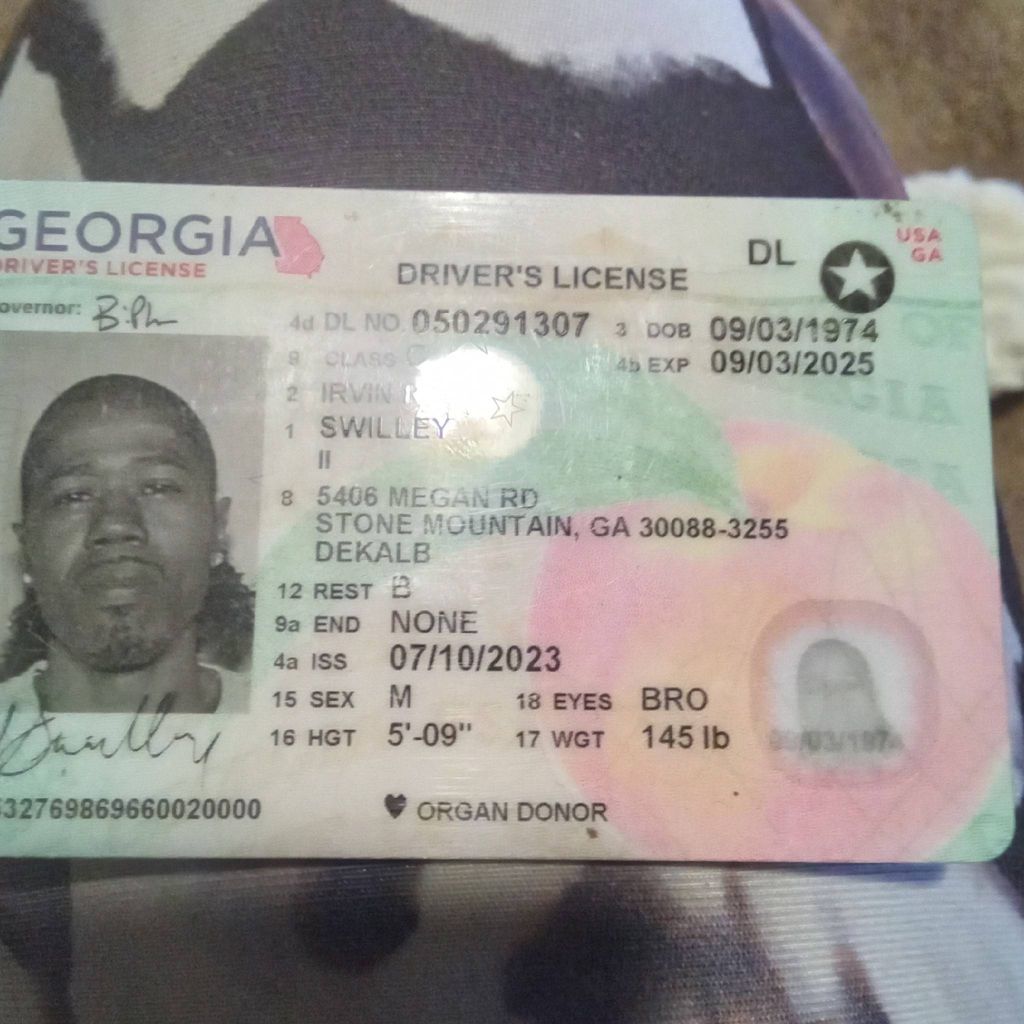
- Printing Quality: The sharpness of images, color accuracy, and consistency of the print are paramount. Imperfections, blurry areas, or incorrect colors are immediate indicators of forgery.
- Watermarks and Security Features: Watermarks are hidden patterns visible only at a specific angle. Their quality, complexity, and positioning are carefully assessed. Similarly, security features like holograms and micro-perforations are analyzed to detect errors or anomalies.
- Paper and Polycarbonate Quality: Identifying the quality of the paper or polycarbonate used is vital. Fake documents frequently exhibit noticeable differences in texture, weight, and resistance. The polycarbonate’s appearance is a key factor.
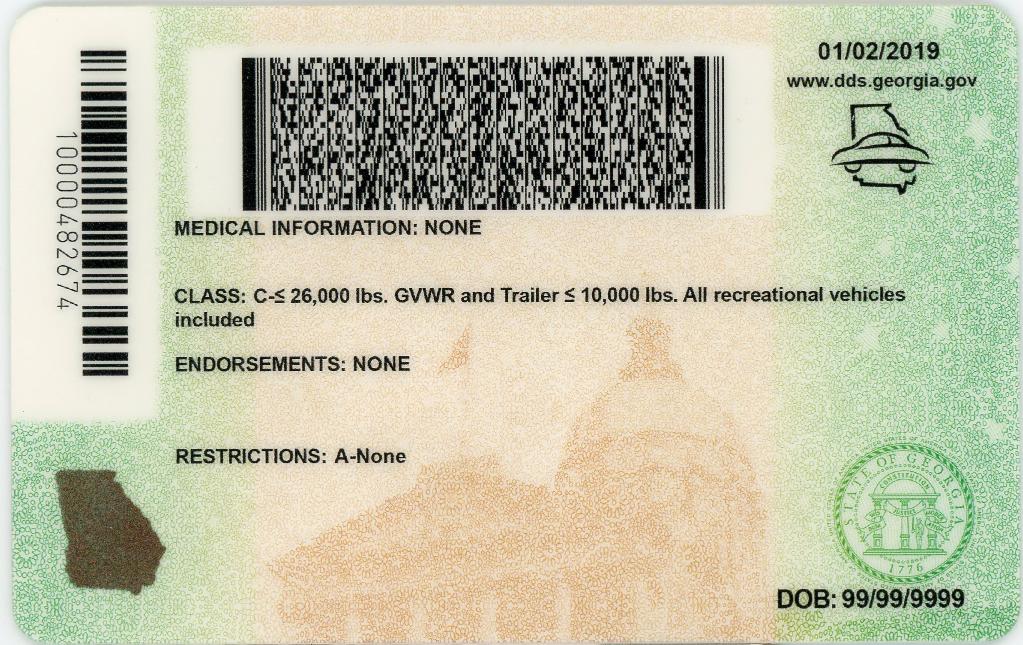
- Magnetic Data Verification: If the document includes a magnetic data chip, it’s verified to ensure it contains the correct information and is compatible with reading systems.
- Data Matching: Information on the document (name, address, date of birth, etc.) is cross-checked with official sources (birth records, DMV, etc.).
- Surveillance Image Verification (SIV): SIV uses imaging technology to detect manipulations on the document, such as insertions, deletions, or alterations.
- Micro-Text and Complex Patterns: Examination of micro-texts and complex patterns to verify their readability and consistency.
fake massachusetts id identical rmv polycarbonate

3. Evolving Security Measures: How Counterfeiters Respond
Authorities and issuing agencies continuously develop security measures to combat counterfeiting. Counterfeiters, in turn, adapt their techniques to circumvent these measures.
- QR Codes and Digital Data: Integrating QR codes and digital data on documents allows for online authentication. However, counterfeiters can replicate these QR codes using manipulation software.
- RFID Technology: The use of Radio Frequency Identification (RFID) chips allows for tracking and authentication. Counterfeiters can replicate these RFID chips, but they aren’t always compatible with reading systems.
- 3D Imaging: 3D imaging creates three-dimensional models of documents, facilitating the detection of anomalies and manipulations.
- Reactive Inks: These inks change color depending on temperature, light, or viewing angle, making forgery more difficult. ( fake nevada id identical dmv polycarbonate )
4. Specific Identification Types: ” fake massachusetts id identical rmv polycarbonate ” (fake utah id identical DMV polycarbonate) and Others
Each state or territory uses unique security measures and materials for its identifications. Counterfeiters adapt their techniques to replicate these specific characteristics. For example, a ” fake utah id identical dmv polycarbonate ” (fake Utah ID identical to DMV polycarbonate) may require specialized skills and equipment to accurately mimic the watermarks, security features, and polycarbonate used by Utah.
5. Legal Implications and Risks
Possessing or using counterfeit identification documents is illegal and carries serious consequences:
- Criminal Charges: Counterfeiters and individuals using fake IDs can face criminal prosecution and imprisonment, along with fines.
- Business Risks: Businesses can be vulnerable to fraud, money laundering, or other criminal activities if they accept counterfeit identification documents.
- Security Threats: Counterfeit identification documents can be used to commit crimes, such as identity theft, fraud, and illegal immigration.
6. Advancements in Authentication Technologies – The Ongoing Arms Race
The battle against counterfeiting isn’t static. Constant advancements in authentication technologies are driving a continuous arms race. Here’s a glimpse of where the fight is headed:
- Spectrographic Analysis: This technique analyzes the chemical composition of the paper and inks, revealing inconsistencies that point to a fake.
- AI-Powered Verification: Artificial intelligence is being developed to automatically analyze images of documents, identifying subtle anomalies that would be missed by the human eye.
- Blockchain Integration: Utilizing blockchain technology to create immutable digital records associated with genuine identification documents – a future where verification is decentralized and highly secure.
7. The Role of Forensic Laboratories
Forensic laboratories play a critical role in authenticating identification documents. They employ specialized equipment and techniques, including:
- Microscopic Examination: Detailed examination of the document’s surface using microscopes to detect inconsistencies in printing, watermarks, and other security features.
- Chemical Analysis: Analyzing the inks and paper to determine their composition and identify any adulterations.
- Spectral Analysis: Examining the wavelengths of light reflected from the document to identify the materials used and detect any alterations.
Conclusion: Vigilance is Key
The ability of counterfeiters to create increasingly realistic replicas underscores the importance of vigilance. By understanding the techniques employed, the evaluation criteria used by experts, and the ongoing advancements in security measures, individuals and organizations can better protect themselves from the risks associated with counterfeit identification documents. The fight against counterfeiting requires a multi-faceted approach, combining technological innovation, regulatory enforcement, and public awareness. Staying informed and maintaining a critical eye are essential in navigating this complex and evolving landscape.